School of Science and Computing
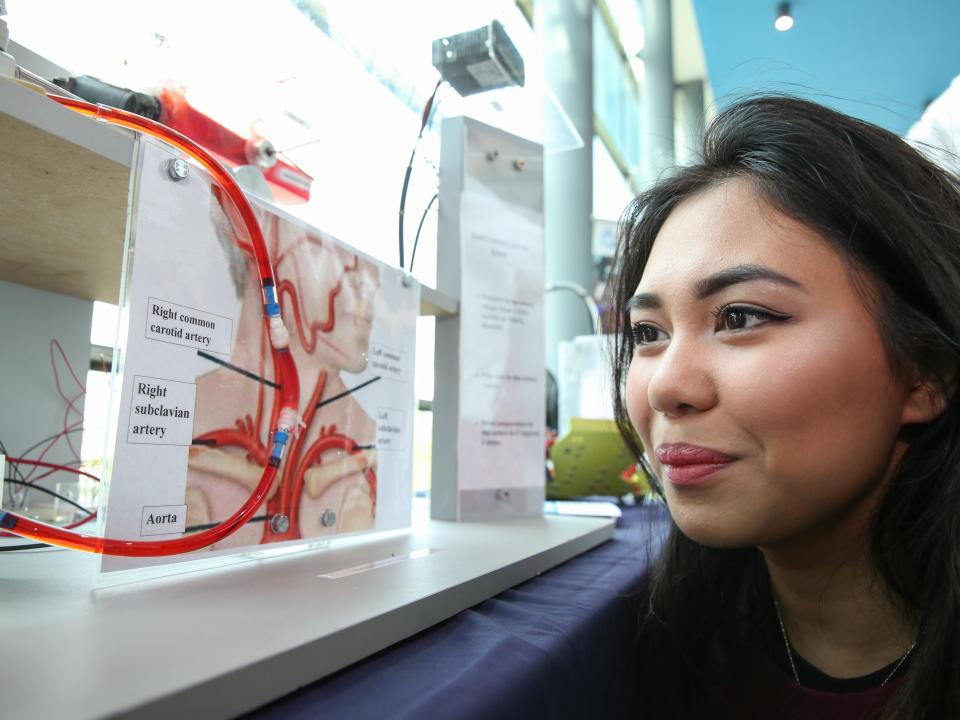
A broad range of courses with a strong emphasis on practical skills.
ATU's School of Science and Computing offers a broad range of undergraduate degree programmes, and is comprised of four departments.
- Analytical, Biopharmaceutical & Medical Sciences
- Computer Science & Applied Physics
- Natural Resources & the Environment
- Sport, Exercise & Nutrition
We place a strong emphasis on active investigation, giving students the opportunity to acquire research skills through practical projects and work placements.
This style of learning helps in developing graduate skills and attributes that are attractive to employers.

Studying Science at ATU

Student Work Placements
Are you interested in taking an ATU science student on work placement?
School of Science and Computing
Head of School (Acting)
Dr Lisa Ryan
Department of Analytical Biopharmaceutical & Medical Sciences
Head of Department
Dr Eugene McCarthy
Department of Computer Science & Applied Physics
Head of Department
Gareth Roe
Department of Natural Resources & The Environment
Head of Department
Dr Ian O’Connor
Department of Sport, Exercise & Nutrition
Head of Department (Acting)
Damien Costello
School Administration
Martina Linnane
Michelle Healy
Sarah Mc Gauley
Suzanne Dempsey
Tel: +353 (0)91 742980
Email: Scienceoffice.galwaymayo@atu.ie